Awareness Materials
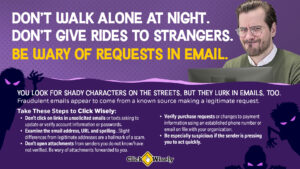
Email Security Awareness: Digital Images


Email Contributes to Most Cyber-related Claims
Most MCIT member cyber-related claims have two factors in common: email and employee behavior. These business email compromise scams can be costly for members in terms of actual dollars lost and time and expense to clean up after the incident.
The below email security digital images help employers remind staff to Click Wisely. The images educate employees about their responsibility for cybersecurity and the simple steps they should take, particularly as it relates to using email.
Ways to Use Email Security Digital Images
- Paste images into emails sent to staff
- Post to intranet landing page
- Print and hang as small posters throughout the facility
- Publish in the employee newsletter
- Display on screen/monitor to kick off a staff or team meeting
- Set as the lock screen image for workstation computers
Tip: Select one message to use at a time and set a schedule for releasing new image (e.g., once every few weeks). This makes it easier for employees to focus on the content.
Download tip: After you click the “download” button, right click on the image that opens and select “Save image as …” option. Then choose where to save the image on your computer.
Topics