Guides and Handbooks
Essentials of Data Security for Public Entities: Second Edition

Fully Updated and Revised Second Edition
 Securing private data is a significant responsibility for local governments. Maintaining data security in the face of real threats, such as threat actors, activists and employee errors, is a challenge that everyone in the organization must work to overcome. “Essentials of Data Security for Public Entities” is a nontechnical handbook for Minnesota local governments to guide them through securing the data and systems they use to carryout their operations and to always Click Wisely.
Securing private data is a significant responsibility for local governments. Maintaining data security in the face of real threats, such as threat actors, activists and employee errors, is a challenge that everyone in the organization must work to overcome. “Essentials of Data Security for Public Entities” is a nontechnical handbook for Minnesota local governments to guide them through securing the data and systems they use to carryout their operations and to always Click Wisely.
Damages from data compromises and cyberattacks to a public entity are often costly, both financially and nonmonetarily. Money is required to correct security issues, restore lost or damaged data, handle legal action and pay regulatory fines. The nonfinancial costs to a public entity can be damaging to an organization’s reputation, lowered morale and loss of the public’s trust.
It is best if your organization has a robust data security program and response plan established before an incident occurs. Now is the time to assess how strong your entity’s programs and plans are before an attack or data compromise happens. Using enterprise risk management methods, this guide is designed to assist in your efforts.
 Guide to Internal Conversations and Policy, Training Development
Guide to Internal Conversations and Policy, Training Development
Maintaining vigilance and being aware of new threats as they emerge is necessary for everyone within your organization. This handbook is not a technical resource. Rather it offers direction to stimulate conversations among the organization’s leadership and provide them with strategies to help the organization secure private data, whether it is electronic or paper in format.
Note: As threats to data security rapidly evolve and systems used by member organizations are varied, this guide often leaves specifics of technical solutions up to the information technology professionals within the organization.
What Is in the Handbook?
- New and fully updated and revised chapters to address current data- and cybersecurity issues (see below for list of chapters), such as data management (retention and destruction), vendor contracts, data hosting, remote work, ransomware, email and text message security, artificial intelligence
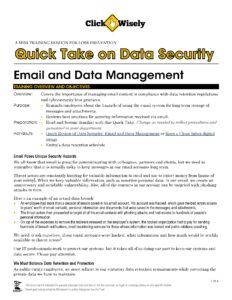
- Recommended policies and best practices: The policies provide a standard and expectation of behavior for all employees to meet, while best practices offer standards the organization as a whole can strive to meet
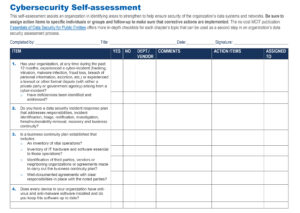
- Checkups: Questionnaires for each topic that organizations can use to assess how they are doing in meeting best practices. These can be used regularly to keep tabs on how well the organization is achieving its improvement goals
- Vetted resources to review for continuous and updated best practices
- Glossary of terms to ensure full understanding of concepts and facilitate conversations with information technology staff
Data Security Is an Entity-wide Effort
This resource should be shared, used and discussed at multiple levels within the organization, including information technology (IT) managers, elected board members, executive directors and administrators, department heads, managers, and others as appropriate (e.g., safety committee).
The Guide’s Chapters
- Introduction: Everyone Plays a Part in Data- and Cybersecurity
- Chapter 1: Data- and Cybersecurity Overview
- Chapter 2: Data Privacy Laws
- Chapter 3: Data Management
- Chapter 4: Vendor Contracts
- Chapter 5: Incident Preparation, Response and Recovery
- Chapter 6: Malware and Ransomware
- Chapter 7: Security Patches and Updates
- Chapter 8: Cloud Data Storage
- Chapter 9: Secure Physical Access and Data Storage Rooms
- Chapter 10: Mobile Devices and Remote Work
- Chapter 11: User Authentication
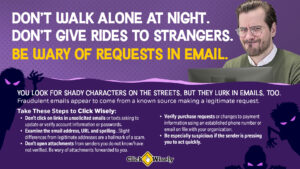
- Chapter 12: Social Engineering: Phishing, Misdirected Payment Fraud, Business Email Compromise
- Chapter 13: Secure Email Practices
- Chapter 14: Secure Internet Browsing
- Chapter 15: Training Employees and Officials
Use in Combination with Other MCIT Resources
Topics