Article
Simple Strategies Shore Up Cybersecurity
Before taking extraordinary and sometimes expensive steps to implement the latest technical options for cybersecurity, an organization should ensure that it has mastered the basics.
4 Best Practices
The Cybersecurity Infrastructure Security Agency of the Department of Homeland Security recommends four key steps to prevent or significantly reduce the risk of data compromises, including ransomware.
- Have a strong password policy that mandates complex and unique passwords. Password management systems can help with the challenges of people forgetting the complicated passwords needed for improved security. Uppercase, lowercase, numbers and symbols are all recommended to be used.
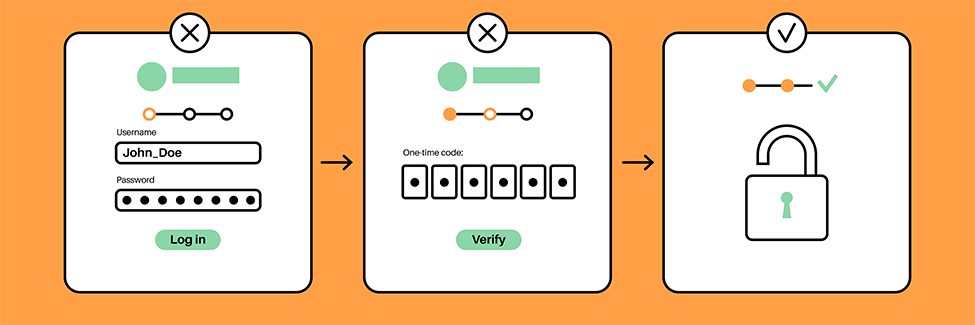
- Implement multifactor authentication. Multifactor authentication requires users to have multiple means to access data, such as first entering a password, then providing a time-limited code that is sent to a mobile phone or a fob.
- Require employees to double check the authenticity of a payment change request (either amount or where payment should be sent). Staff should check using methods that are currently on record with the member, such as the phone number, not the one included in the request for the change. See Avoid the Lure of Phishing Scams for more.
- Repeatedly train employees on how to identify phishing or fraudulent messages. Most malware comes from phishing. Malware, including ransomware, allows threat actors to gain access to an organization’s network and data. Ongoing training about how to spot potential fraud and what to do about it is key to limiting malware and misdirected payments. Certain vendors offer simulated phishing attacks and training that help keep staff aware of and on guard for attacks.
- Require software updates. Often malware targets vulnerabilities in software that is only fixed via updates. Many updates are made by IT without the end user’s knowledge, though with many employees working from home or using mobile devices for work, this becomes even more crucial. The endpoints, which are the specific computers, laptops, tablets or other mobile devices, in addition to the main network servers both need to be updated to maintain security. Staff should not be permitted to delay updates indefinitely.
MCIT Recommendations
Based on actual member cyber claims, MCIT encourages members to implement these additional data compromise risk management strategies:
- Adhere to the data retention and destruction schedule: The less data that can be compromised limits the magnitude of an incident.
- Clean out email: Email is highly vulnerable to hacking and should not be used as a storage system. Employees should limit how many emails they keep in the email system, particularly those that contain private and personal data. Remind staff that they can save files for future reference in a more secure area on the organization’s network.
- Create a culture of open communication that makes employees comfortable reporting mistakes and suspected attacks. The quicker the member knows of a potential problem, the faster it can be investigated and addressed, minimizing the fallout.
- Support cybersecurity infrastructure such as segmented networks and segregated backups. These two structures allow for better containment of an attack’s effects and to return to operations after an incident, so budget for these necessities.
Topics



